If your business is still relying on traditional antivirus software for endpoint protection, you’re not alone — and you’re not necessarily doing something wrong. Antivirus has been the default security tool for decades, and for good reason: it works, it’s inexpensive, and it’s easy to deploy.
But the threat landscape your antivirus was designed to fight no longer exists.
Today’s cyberattacks — the ones actually hitting Australian businesses — don’t leave signatures for antivirus to catch. They use fileless malware that lives entirely in memory. They hijack legitimate Windows tools. They move laterally across networks for weeks before striking. They are specifically engineered to look like normal business activity until it’s too late.
According to recent cybersecurity research, 82% of modern data breaches use techniques that bypass traditional antivirus entirely — including fileless malware, living-off-the-land attacks, and zero-day exploits that leave no file signatures behind.
This is the gap that Endpoint Detection and Response (EDR) was built to close. This guide explains the differences clearly, helps you work out which solution your business actually needs, and shows you what best-in-class EDR protection looks like in practice.
What Is Traditional Antivirus?
Traditional antivirus software operates on a simple principle: compare files against a database of known malware signatures. When a file is downloaded, opened, or executed, the antivirus checks it against a continuously updated list of known bad files. If there’s a match — it blocks it.
This approach is fast, lightweight, and highly effective against known threats. For the first two decades of the commercial internet, it was largely sufficient.
What antivirus is good at:
- Detecting and removing known malware, viruses, and ransomware strains
- Scanning email attachments and downloads for recognised threats
- Running quietly in the background with minimal system impact
- Low cost — typically a flat per-device annual fee
Where antivirus falls short:
- It cannot detect threats it hasn’t seen before (zero-days)
- It is completely blind to fileless attacks that never write to disk
- It cannot stop attackers who use legitimate system tools (PowerShell, WMI)
- When it blocks a file, it provides no context: no timeline, no investigation path, no indication of how far an attacker has already moved
- It reacts after a threat has arrived — it cannot hunt for threats that are already present
In short: antivirus is reactive. It waits for a known threat to appear, then acts. Against modern adversaries who specifically design their techniques to be unknown and file-free, it often never fires at all.
What Is EDR?
Endpoint Detection and Response (EDR) is a fundamentally different approach to endpoint security. Rather than scanning for known malicious files, EDR continuously monitors everything happening on an endpoint — every process, every network connection, every file change, every user action — and uses behavioural analysis and AI to identify threats based on what they do, not what they look like.
Think of the difference this way: traditional antivirus checks whether a visitor is on a list of known criminals before letting them in. EDR watches what every visitor does once they’re inside — and raises the alarm if anyone starts acting suspiciously, regardless of whether they’re on any list.
What EDR does:
- Continuous monitoring: Records a complete, real-time telemetry stream from every endpoint — processes, network activity, registry changes, file modifications, user logins
- Behavioural detection: Identifies anomalous patterns that indicate attack activity — mass file encryption (ransomware), lateral movement, credential dumping, unusual admin tool use
- Automated response: Can automatically isolate a compromised endpoint, kill a malicious process, or roll back changes — at machine speed, before a human analyst even sees the alert
- Threat hunting: Allows security analysts to proactively search for indicators of compromise across all endpoints simultaneously
- Forensic timeline: Provides a complete reconstruction of an attack’s path — when it entered, how it spread, what it touched — essential for incident response and compliance reporting
- Zero-day and fileless protection: Because detection is behaviour-based, EDR can catch threats with no known signatures
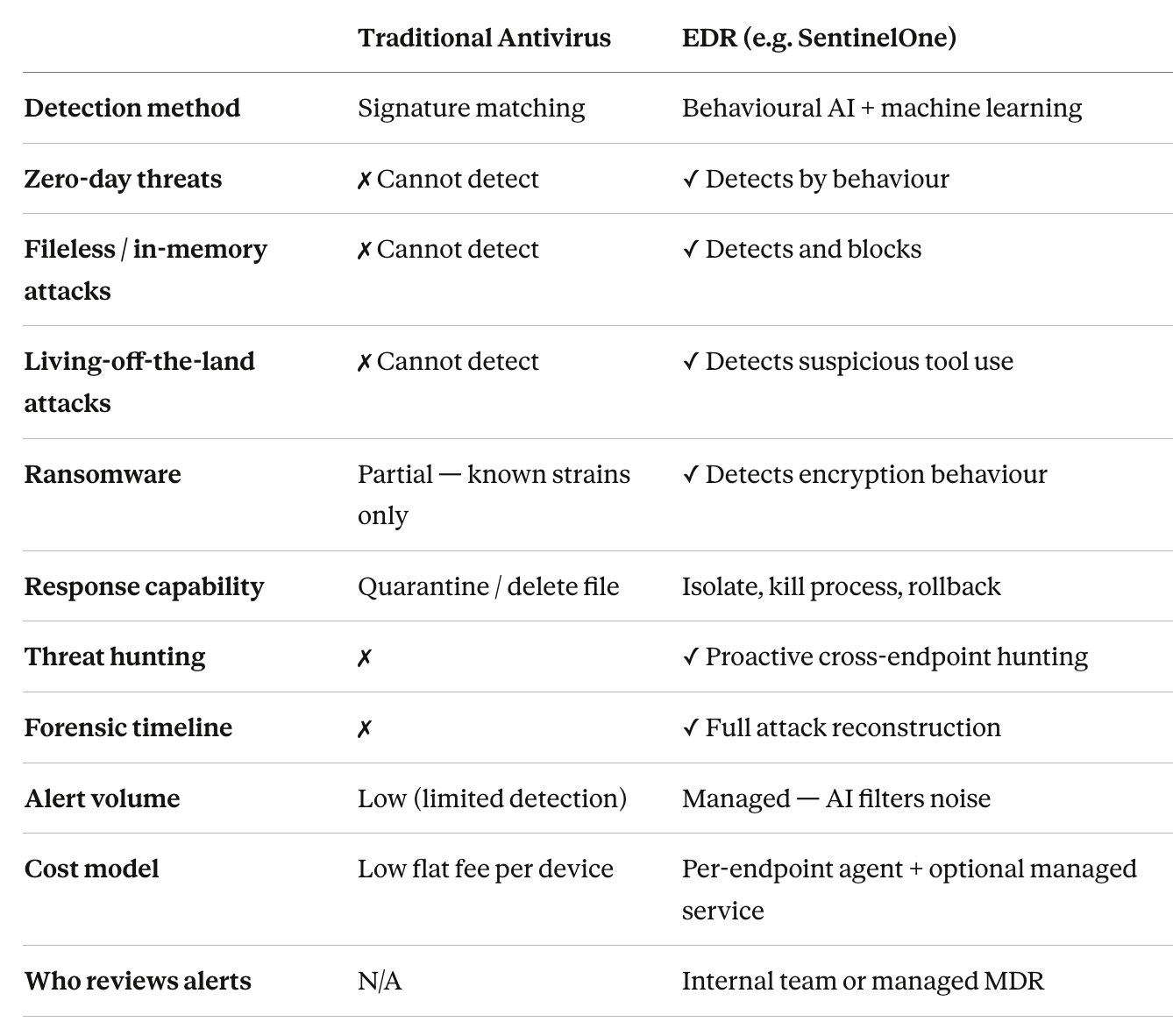
Antivirus vs EDR: Side-by-Side Comparison
Why Traditional Antivirus Is No Longer Enough in 2026
The threat actors targeting Australian businesses in 2026 are not the script kiddies of the early internet. They are professional, organised, and patient.
Attackers now use living-off-the-land techniques, customise ransomware per target, and have dissolved the network perimeter through remote work and cloud adoption. A business relying solely on antivirus today is defending a 2026 threat landscape with 2008 tools.
The ASD’s Annual Cyber Threat Report 2024–25 makes clear that ransomware remains the most financially damaging threat to Australian businesses — with average costs per incident reaching A$97,200 for medium-sized businesses. The defining characteristic of modern ransomware: it almost never triggers a signature-based antivirus alert before detonating, because the initial access, lateral movement, and privilege escalation phases all use legitimate tools.
Remote work has expanded the attack surface significantly — with employees working from distributed locations, the traditional network perimeter has dissolved, making each endpoint a potential entry point for attackers. Meanwhile, sophisticated threats including advanced persistent threats, fileless malware, and zero-day exploits are specifically designed to bypass conventional security measures.
Regulatory compliance and cyber insurance requirements are increasingly mandating advanced endpoint protection beyond traditional antivirus, with multiple frameworks including PCI DSS 4.0 and NIST Cybersecurity Framework 2.0 now requiring continuous monitoring and behavioural detection capabilities. Many insurers now require EDR as a minimum baseline for coverage, making legacy antivirus-only environments effectively uninsurable against modern cyber risks.
What Makes SentinelOne the EDR of Choice?
Not all EDR platforms are equal. For Australian businesses evaluating options, SentinelOne’s Singularity Platform stands apart on every meaningful metric — and the evidence is independent, not marketing copy.
MITRE ATT&CK Evaluations: The Industry Gold Standard
The MITRE ATT&CK Evaluations are the most rigorous independent assessment of endpoint security products available. In 2024, MITRE made the testing even more stringent: analysts personally operated each vendor’s console as a real SOC would, preventing any vendor from gaming results.
SentinelOne’s Singularity Platform achieved 100% detection and zero detection delays in the 2024 MITRE ATT&CK Evaluations: Enterprise — detecting all 16 attack steps and 80 substeps across Windows, Linux, and macOS environments. Singularity also generated 88% fewer alerts than the median across all vendors evaluated, significantly reducing alert fatigue for security teams.
This was not a one-off result. For the fifth consecutive year, SentinelOne’s Singularity Platform achieved 100% detection and zero detection delays in the MITRE ATT&CK evaluation, successfully detecting all staged attacks across every phase of simulation.
Gartner Recognition
SentinelOne has been named a Leader in the Gartner Magic Quadrant for Endpoint Protection Platforms for five consecutive years — a recognition reserved for vendors who combine strong execution with a compelling vision. On Gartner Peer Insights, it holds a 4.8/5 rating with 96% of reviewers saying they would recommend it.
What SentinelOne’s Singularity Platform Covers
- AI-powered EDR — Behavioural detection across all endpoints, automatically stopping threats before they spread
- XDR (Extended Detection and Response) — Goes beyond endpoints to correlate data across cloud, identity, and network layers for enterprise-wide visibility
- Storyline™ technology — Automatically connects benign and malicious events into a complete, readable attack narrative — saving analysts hours of manual investigation
- Autonomous response — Isolates compromised devices, kills malicious processes, and rolls back ransomware changes at machine speed
- Distributed AI — Every endpoint runs AI locally, so protection works even without a network connection
- Cross-platform coverage — Full protection across Windows, Linux, and macOS
Protect Your Endpoints Before the Next Attack
The gap between antivirus and EDR is no longer theoretical — it’s measured in breach statistics, ransom payments, and recovery costs affecting Australian businesses every month.
The good news: getting protected with enterprise-grade AI-powered EDR through SentinelOne is faster and more affordable than most businesses expect — and ANP Technology handles everything from deployment to ongoing support.
Contact the ANP Technology team today for a free endpoint security consultation. We’ll assess your current setup and show you exactly what SentinelOne can do for your business.📧 Contact us: https://www.anptech.com.au/contact-us/